In our earlier posts, we have discussed IP completely. We said that every device that wants to join a network, gets an IP. But how do these devices know which IP they should get? This is when DHCP can help us.
IP Assignment
There are two ways of assigning IPs to devices:
- Statically: you have to go over all the IPs that are used in the network to make sure which one is not taken and then assign a non-taken IP to the device. You should also be careful to choose an IP that has the correct Net ID in order to be visible in that network.
- Dynamically: This way means that when a device connects to a network, an IP will be assigned to it automatically. But what does this automatic assignment?
DHCP
A DHCP server is a network server that automatically assigns IP addresses, default gateways and other network parameters to client devices. It is based on the Dynamic Host Configuration Protocol (DHCP) to respond to broadcast queries by clients.
So, DHCP can simplify the IP assignment and management in a network. Imagine you have 30 different client devices in a place and you want all of them to be in the same network. To do this, you have to assign IPs with the same Network ID to all of them. Obviously it takes a lot of time to do this manually that is why instead of going over every device and assign an IP to them one by one, you can have a DHCP to do this for you.
How does it work?
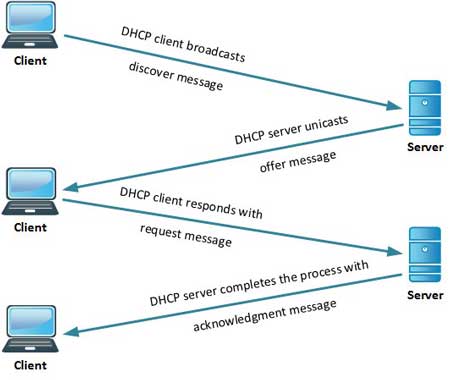
The stages of IP assignment by DHCP are called DORA: Discovery, Offer, Request, and Acknowledgment.
- Discovery: The client sends a broadcast request to find a DHCP server.
- Offer: After the DHCP Server receives the discover message it suggests the IP addressing offering to the client by unicast.
- Request: Now after the client receives the offer it sends a request message to the server officially this time by unicast.
- Acknowledgment: Server sends an ACKNOWLEDGE message confirming the DHCP lease to the client. Now the client is allowed to use new IP settings.
The security risk of using DHCP
Using a DHCP server is not all good and it has its cons too.
The DHCP protocol requires no authentication so any client can join a network quickly. Because of this, it opens up a number of security risks, including unauthorized servers handing out bad information to clients, unauthorized clients being given IP addresses and etc.
Since the client has no way of validating the authenticity of a DHCP server, it can cause denial-of-service attacks or man-in-the-middle attacks where a fake server intercepts data that can be used for malicious purposes. Conversely, because the DHCP server has no way of authenticating a client, it will hand out IP address information to any device that makes a request. A threat actor could configure a client to continually change its credentials and quickly exhaust all available IP addresses in the scope, preventing company endpoints from accessing the network.
We hope you enjoyed this post. If you did, you can visit our blog for more.





